AWS Outage Created “Perfect Storm” for Social Engineering Attacks
Last week Amazon Web Services (AWS) went down worldwide, including here in Canada, causing a ripple effect, from governments and local municipalities, to enterprises, small businesses and the individuals who rely on these services daily.
AWS is a cloud-based service thousands of major companies use to not only store their data, but run their apps and software for many critical business services.
Whether basic communications using apps such as Snapchat, Signal and Reddit to airlines such as Delta and United reporting disruptions to their customer facing operations, when these services go down it highlights the reliance on just a few cloud services companies (AWS, Microsoft Azure, and Google Cloud) to ‘run the country’ so to speak.
The AWS outage has further impacted shopping websites, banking apps, and even streaming and smart homes devices.
And while organizations scramble to ensure business operations continue to run, it’s also an opportunity for individuals to do a quick check-in on their own cyber hygiene.
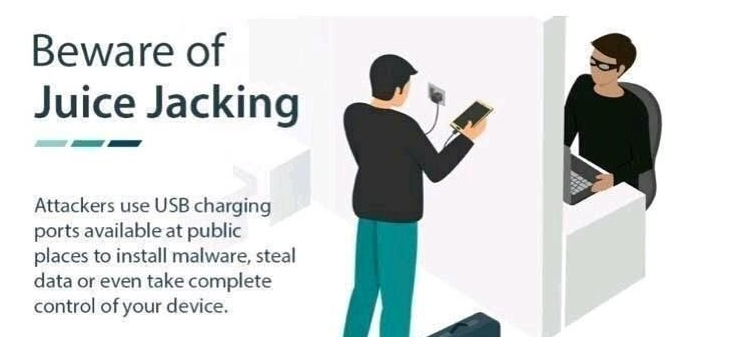
Cybercriminals and hackers can easily take advantage of these types of outages to deploy an array of social engineering attacks.
Whether in the office or at home, nothing is more frustrating than losing the ability to access files and documents, and communicate with business associates or loved ones, especially in an emergency or crisis.
Hackers who rely on mass urgency and panic will see this as an opportunity to take advantage of people’s heightened emotions with phishing emails offering to “fix” the issue and get you back online and into your accounts or apps.
But in reality, these scammers are looking to steal your personal information, such as login credentials by tricking you into updating your software or resetting your password.
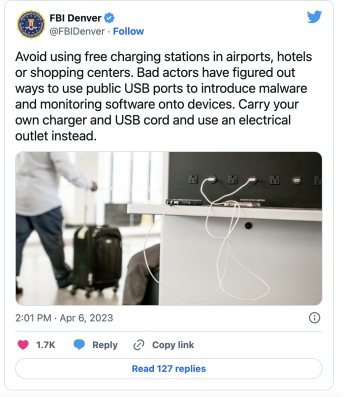
During major outages, users should avoid clicking on any links in emails, texts and pop-ups claiming to be able to fix the outage.
Additionally, double check that any alerts or update messages from organizations, such as your bank or payment apps, are verified from the official website or app.
This is the time to make sure you are using a strong password and multifactor authentication to prevent any unauthorized access to your accounts.
Delay Things
However, individuals should also delay making sensitive transactions, such as major financial transactions, resetting your password, or installing critical software updates, until the service in question has been announced as officially restored.
Furthermore, when the service disruption has ended, users should also monitor any affected accounts for unusual activity, discrepancies, and duplicate or fraudulent transactions.
Finally, this is an excellent reminder for individuals to make sure they have a back-up system in place to access important documents and for communications.
This can be as easy as keeping a secondary email account or even a back-up mobile phone. For the Silo, Stefani Schappert.
ABOUT THE AUTHOR
Stefanie Schappert, MSCY, CC, Senior Journalist at Cybernews, is an accomplished writer with an M.S. in cybersecurity, immersed in the security world since 2019. She has a decade-plus experience in America’s #1 news market working for Fox News, Gannett, Blaze Media, Verizon Fios1, and NY1 News. With a strong focus on national security, data breaches, trending threats, hacker groups, global issues, and women in tech, she is also a commentator for live panels, podcasts, radio, and TV. Earned the ISC2 Certified in Cybersecurity (CC) certification as part of the initial CC pilot program, participated in numerous Capture-the-Flag (CTF) competitions, and took 3rd place in Temple University’s International Social Engineering Pen Testing Competition, sponsored by Google. Member of Women’s Society of Cyberjutsu (WSC), Upsilon Pi Epsilon (UPE) International Honor Society for Computing and Information Disciplines.
ABOUT CYBERNEWS
Friends of The Silo, Cybernews is a globally recognized independent media outlet where journalists and security experts debunk cyber by research, testing, and data. Founded in 2019 in response to rising concerns about online security, the site covers breaking news, conducts original investigations, and offers unique perspectives on the evolving digital security landscape. Through white-hat investigative techniques, Cybernews research team identifies and safely discloses cybersecurity threats and vulnerabilities, while the editorial team provides cybersecurity-related news, analysis, and opinions by industry insiders with complete independence.
Cybernews has earned worldwide attention for its high-impact research and discoveries, which have uncovered some of the internet’s most significant security exposures and data leaks. Notable ones include:
- Cybernews researchers discovered multiple open datasets comprising 16 billion login credentials from infostealer malware, social media, developer portals, and corporate networks – highlighting the unprecedented risks of account takeovers, phishing, and business email compromise.
- Cybernews researchers analyzed 156,080 randomly selected iOS apps – around 8% of the apps present on the App Store – and uncovered a massive oversight: 71% of them expose sensitive data.
- Recently, Bob Dyachenko, a cybersecurity researcher and owner of SecurityDiscovery.com, and the Cybernews security research team discovered an unprotected Elasticsearch index, which contained a wide range of sensitive personal details related to the entire population of Georgia.